In an era of total tracking and increased cybersecurity systems, the concept of a digital browser fingerprint is becoming not just something distant and obscure, but very much relevant.
But what exactly is a digital browser fingerprint? Let’s get to the bottom of it!
Your browser leaves a unique “footprint” every time you visit a site – a set of characteristics of your device and software environment that sites use to recognize you. This is the browser fingerprint and can be compared to digital biometrics: just as a fingerprint uniquely identifies a person, the combination of browser settings is virtually unique for each user.
Briefly: who needs your digital browser fingerprint and why
Is it that important? From the perspective of a simple internet user, a browser fingerprint allows you to follow them online more closely. Businesses are actively using browser fingerprints for analytics and targeting. Advertising networks, with the help of these fingerprints, can track visitors even without cookies, and large platforms(social networks, marketplaces) can identify users with multiple accounts.
Services are beefing up their anti-fraud systems: banks and payment services check device settings at login to prevent fraud. If you log into your account from a new device with a different browser fingerprint, the security system may freeze your account and ask for identity verification, suspecting hacking.
And advertising platforms like Facebook are very sharp at blocking dozens of accounts if they see that they are launched from the same browser and device by a matching browser fingerprint.
After all, this is a challenge to the user’s personal anonymity. Traditional privacy methods (clearing cookies, incognito mode) no longer guarantee invisibility: your browser’s unique settings will give you away to the site all over again.
How fingerprint tracking works: principle
The mechanism of browser fingerprinting is based on the collection of many disparate pieces of information about your device and browser, which together produce a unique combination – the browser fingerprint.
When you visit a website, it can use JavaScript scripts to ask your browser for various parameters: OS version, screen resolution, font list, and dozens of others.
Your digital passport
Individually, each of these fields does not reveal the user’s identity and seems harmless. The combination of these data is a kind of digital passport. Modern server-side algorithms gather all the parameters together and calculate a unique hash code, which is the browser fingerprint.
What about cookies? How are they different from browser fingerprints?
| Cookie files | Browser Fingerprint |
| Stored on the user’s device (in the browser), can be deleted or blocked manually. | Not saved on the device; generated dynamically on the server from browser settings. User does not see or control the process. |
| Contains an explicit identifier (ID) assigned by the site. Use is regulated by law (cookie consent required). | Implicit identifier calculated from technical data. There is little or no direct regulation, collection is unannounced. |
| Easy to reset: deleting a cookie “resets” the visit history for the site. | Persistent: with the same device settings, the site recognizes the visitor without a cookie (even in incognito mode or after clearing the browser). |
In other words, the digital fingerprint of the browser is generated on the fly and compared with previously saved records on the server. If the user has already visited the resource, the system will compare the freshly collected browser fingerprint with the database: if it matches, you will be recognized as an “old” client, if it does not match, you will be recognized as a new (or suspicious) client.
All this happens in a hidden way: there are no pop-ups or warnings. This is what makes fingerprinting so valuable for tracking: it works invisibly and does not depend on the user’s actions.
Deep Dive: what parameters can be included in a digital browser fingerprint
Modern scripts are able to collect dozens of browser and device characteristics. including:
1. IP address.
A basic parameter that determines the approximate location and provider. Of course, it is difficult to unambiguously recognize a person’s identity from a single IP address, but it gives away the user’s country and city. Many antifraud systems start checking from the IP address.
2. User-Agent and other HTTP headers.
User-Agent – a string that is passed by the browser at each request. It contains the browser name and version, operating system type, device model (for mobile), and engine information.
Other headers, such as Accept-Language or Accept-Encoding, contain information about your browser and OS settings. The set and order of headers may differ between browsers, which is also taken into account in the footprint.
3. Screen resolution and display settings.
The browser reports the width and height of the screen (in pixels), the color depth, and the current window size. These numbers help the site to adapt the interface, but also allow you to understand what kind of device you have (1920×1080 resolution indicates a standard Full HD monitor).
It also analyzes pixel density (devicePixelRatio), which distinguishes a Retina display on a Mac laptop from a regular PC screen at the same nominal resolution. The combination of resolution and density is in most cases unique to a particular device model.
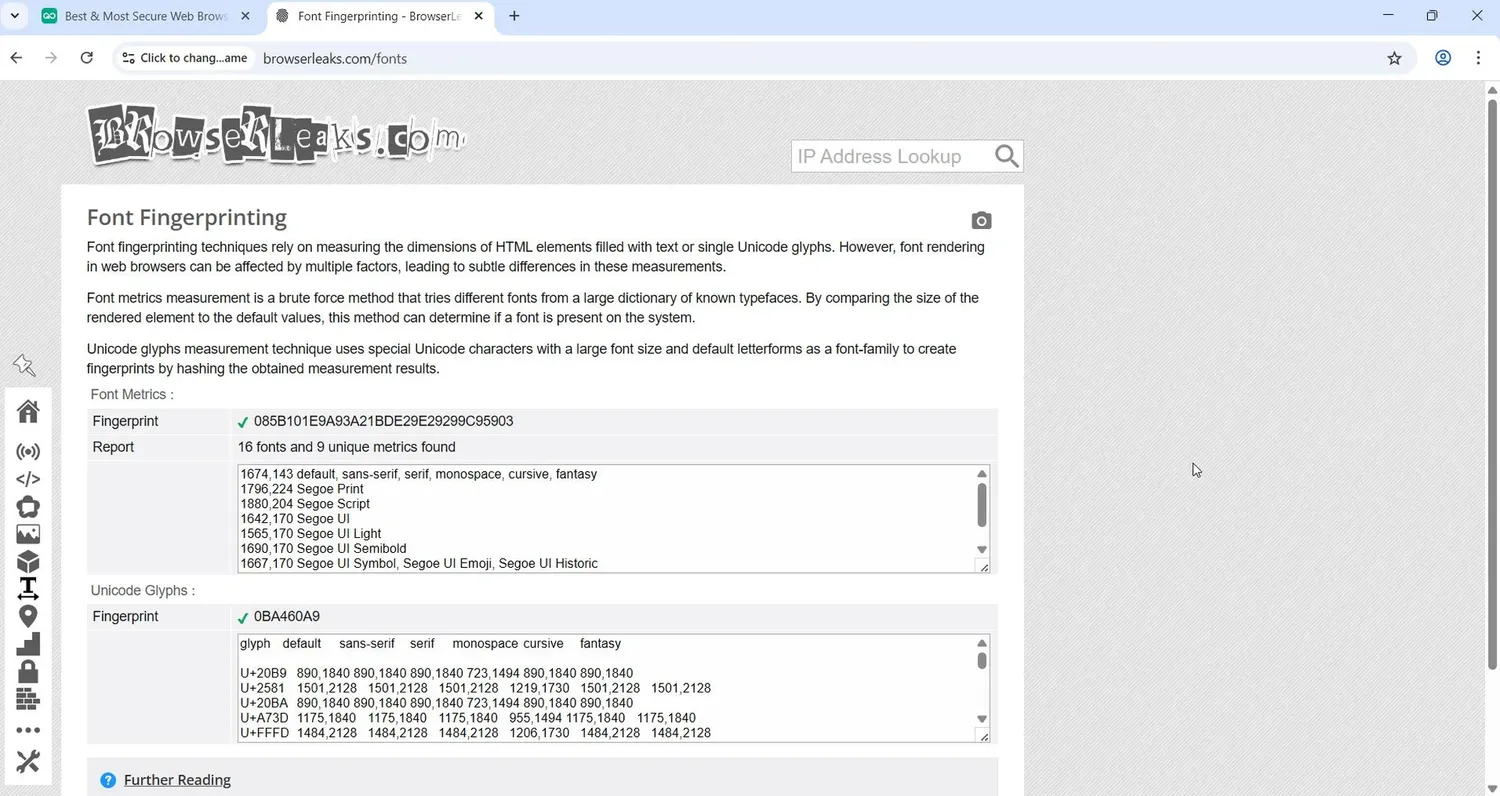
4. System Fonts.
Every operating system has a set of pre-installed fonts. Standard fonts (Arial, Times New Roman, etc.) are available everywhere, but system fonts differ. In Windows, for example, Segoe UI is available, and in macOS – San Francisco. The site can determine through a hidden script what fonts are installed in the system.
The unique font list actually “highlights” your OS and even its version: if the browser fingerprint is claimed to be macOS, but Windows headsets are visible in the font list, antifraud will suspect spoofing. In addition, the rendering of the same font may differ between OSes – this is also part of the fingerprint.
5. Time zone.
The time offset relative to UTC is transmitted. It is used to tell the site what region the user is in. The time zone should be logically combined with the IP geolocation: if the IP belongs to France (UTC+1), but the browser time zone is UTC+8, questions arise.
Such unsynchronizations greatly increase the “anonymity” (read suspiciousness) of the print.
6. Language settings.
This includes the interface languages and browser locale settings specified in the system. For example, navigator.language and the navigator.languages array show the user’s primary and secondary languages.
As with the time zone, it is better to choose the language according to the IP you are using and the target audience. If the account is designed for a Spanish-speaking country and the browser is fully Russianized, it looks strange.
7. Hardware characteristics (CPU, RAM).
The browser’s hidden properties contain information about the device: the number of logical processor cores (hardwareConcurrency), the amount of installed memory (deviceMemory).
These numbers allow us to draw conclusions about the type of device and inconsistencies are also noticeable here: if the device is claimed to be Android, and hardwareConcurrency = 16 – it is a suspiciously “powerful” phone.
8. Graphics environment data (Canvas and WebGL).
Browsers provide APIs for drawing graphics that leave a unique footprint. Canvas is an HTML5 component that allows you to draw an invisible image and get its “signature” (hash). Minimal differences in video card, drivers and rendering algorithms result in a different Canvas hash on different devices. WebGL is an interface for 3D graphics that works directly with the GPU.
Through WebGL the script gets information about the video card (model, manufacturer, driver version). WebGL fingerprints by themselves are already unique, and together with Canvas they give a powerful graphical fingerprint that is hard to fake without disabling features.
9. Audio imprint.
Another hidden channel is the HTML5 Audio API. The site generates inaudible sound of a certain frequency and processes it through the device’s audio processor, and then reads the resulting values.
Differences in sound drivers and “hardware” cause the output to vary from machine to machine. The resulting browser fingerprint AudioContext can distinguish devices almost as confidently as Canvas. While this method is still rarely used, it adds an extra layer of uniqueness.
10. List of browser plug-ins and extensions.
Historically, browsers allowed you to get a list of installed plugins (Flash, PDF viewers, etc.). Nowadays plugins are limited (Flash is disabled, NPAPI plugins are removed), but the very fact – whether the browser has built-in plugins – can affect the footprint.
Extensions are not directly visible to sites, but some of them can indirectly affect the browser footprint (blocking certain scripts or adding special headers).
11. Local Storage and settings.
Whether cookies are enabled and Web Storage mechanisms are available (LocalStorage, SessionStorage) whether the Do Not Track flag is set. The paradox is that if the DNT flag is enabled, it adds additional uniqueness to the print.
The set of APIs supported by the browser (IndexedDB, Service Workers, etc.) and even minor customizations (how prohibited requests are handled) are all small touches to the device profile that enhance its uniqueness.
12. WebRTC and network interfaces.
WebRTC (technology for p2p communication) can give out your real IP address even when working through a proxy or VPN. The script is able to query WebRTC for a list of network interfaces and get local IP (inside the network) and external IP.
Thus, the browser fingerprint can include two addresses – masked and real. WebRTC can determine the nature of the network (mobile, Wi-Fi, proxy, etc.) by indirect signs (connection delay, address type).
13. Media Devices.
Using the browser API you can find out how many cameras, microphones, audio outputs are connected in the system.
For example, a laptop usually has 1 webcam and 1 microphone, while a desktop PC may not have a camera at all. The number of media devices (0, 1, 2…) adds another parameter to the footprint.
14. Permissions API.
Anti-fraud systems analyze the list of permissions available to the browser: whether notifications can be shown, whether access to the camera, microphone, geolocation, clipboard is allowed.
The statuses of these permissions vary between systems and browsers, so a mismatch will look suspicious.
15. Touch Signals and Pointer Events.
Number of possible touches (maxTouchPoints), multitouch support, pointer types, and touch gesture processing all form an additional layer of fingerprinting.
Mobile devices have predictable metrics, and if a smartphone is claimed but there are no touches, the system will flag an anomaly.
16. Signs of automation and WebDriver operation
This is a behavioral anti-bot signal, it is part of the browser’s extended fingerprint. Even with the navigator.webdriver flag turned off, antifraud will detect Selenium, Puppeteer or Playwright through indirect signs: abnormal mouse events, sequence of user actions, lack of typical features typical of real Chrome.
Any traces of automation increase the suspiciousness of the profile.
17. TLS fingerprint and network connection parameters.
The browser and the device form their unique TLS fingerprint: the cipher order, ClientHello, a set of extensions is standard procedure during normal operation. If the network fingerprint does not match the declared browser or device, the profile immediately falls into the “gray zone”.
18. Features of HTTP/2 and HTTP/3.
Browsers form HTTP2/3 headers, pseudo-headers and frames differently. Antifrod knows the standard order and logic for Chrome, Safari, Firefox, Edge. And here is one more touch to the overall picture.
19. Network Information API.
From the available network data, you can determine the type of connection (Wi-Fi, mobile network), the true latency, throughput, and the nature of connection hops.
If a mobile proxy is used, but the network is defined as Ethernet with zero packet loss – the behavior looks unreliable.
20. CSS rendering and engine features.
Even the same browser renders CSS differently on different OSes. Element sizes, shadows, anti-aliasing, block metrics calculation all create a unique, hard-to-fake browser footprint that adds uniqueness to the overall picture.
21. WebGPU.
WebGPU provides even deeper access to the GPU than WebGL. It reads the GPU’s features, architecture, parallel computation, and response to micro-loads.
These signals are actively implemented in anti-fraud systems and allow the device to be identified more accurately than Canvas.
As technology evolves, new sources of data are also emerging, from device battery information to patterns of user behavior (e.g., typing dynamics or mouse movements).
Why a digital browser fingerprint is used
Personalization and analytics
For website owners, fingerprinting is a way to recognize a visitor even without explicitly logging into an account. It allows you to account for unique users: how many times you logged in, from what devices, how long you stayed on the site.
Based on the footprint, they form behavior analytics: they build a “map” of clicks and views, find repeat visits.
Advertising and targeting
Marketing platforms are actively using browser fingerprints for more accurate ad targeting. While in the past the main binding was a cookie and IP address, now the fingerprint provides a stable identifier that is difficult to fake.
Advertisers can learn that a visitor without authorization has visited the site for more than the first time and show them personalized ads or special offers.
A digital fingerprint helps to combine the actions of one user in different sessions and even on different sites. This is important for retargeting: you can clear cookies, but the network advertising script will recognize you by technical parameters and will continue to show ads “by interest”.
For ad networks, this is a valuable tool – it increases display accuracy and the likelihood of conversions.
Antifraud and security
One of the most useful functions of fingerprinting is fighting online fraud. Anti-fraud systems of banks, payment services, online games, and advertising platforms collect fingerprints of devices to detect suspicious activities:
Online Banking remembers a “trusted” device by fingerprint. If someone tries to log in to your account from another computer, the system will notice the new device and may request additional verification or block the login.
 Social networks and gaming platforms track the creation of multi-accounts. If one user makes dozens of profiles, but they all have the same or similar fingerprint (same machine, same browser), the system associates them and applies sanctions.
Social networks and gaming platforms track the creation of multi-accounts. If one user makes dozens of profiles, but they all have the same or similar fingerprint (same machine, same browser), the system associates them and applies sanctions.
Ad platforms and ad cabinets calculate fake account farms through matching fingerprints.
Antifraud analyzes not only the fingerprint itself, but also the dynamics of its changes. Usually, for an average user, the set of parameters is stable (it changes gradually when the browser is updated or the device is changed).
If the system sees that one account has one browser fingerprint today, another tomorrow, and a third the day after that, this is a clear signal of spoofing or automation. This is how multi-accounts are detected, as well as attackers who regularly change their environment to circumvent blocking.
How to check your browser fingerprint
Find out what kind of browser footprint you show to sites can be done with the help of special checkers. They collect the main parameters and show them, additionally scoring the uniqueness. In particular:
- Whoer.net и IPhey.com – Comprehensive anonymity checking services that show your IP, DNS, proxy status, key browser settings and provide an overall privacy “rating”.
- BrowserLeaks.com – is a service with a set of detailed tests. Broken down into sections: IP, WebRTC, Canvas, Fonts, Audio, Plugins, etc. Helps you test every aspect of the footprint consistently. BrowserLeaks gives the most technical picture of your fingerprint.
- Pixelscan.net – analyzes the integrity of a fingerprint. It calculates the score of the digital fingerprint and concludes how unique and suspicious your profile is. If there are inconsistencies in the combination of data, Pixelscan will indicate this in the report.
- CreepJS – The service checks different components of your browser footprint, showing you where you might have subtle issues.
For a complete picture, use several checkers, as each of them emphasizes its own metrics. If one resource shows that you are “unique among 1,000 devices”, and another one gives you 80% anonymity, that’s fine.
Pay attention to inconsistencies: whether your time zone and language match your IP, whether your WebRTC leak is flagged, whether your font list looks suspiciously empty or “alien”. The goal is for your fingerprint to look as much like a typical footprint of a regular user from the selected location as possible.
How to change your digital browser fingerprint
Now that you know that the site “sees” your digital profile, the question arises: can your fingerprint be changed or hidden? In short, yes. There are several approaches:
Change your browser or device.
The easiest option is to log in from another browser (computer or phone). Chrome, Firefox, Safari profiles have different User-Agent and slightly different characteristics, so the fingerprint will be different. For some simple cases this together with a proxy is enough.
Browsers like Brave can partially block tracking. Changing your device is a radical method, but not always convenient. Besides, blocking tracking itself can be a security trigger on the same social network sites.
Manual environment setup.
Theoretically, you can independently change many of the parameters by which the fingerprint is generated:
-
- change the system settings (time zone, interface language) for the required region;
- install additional fonts or remove unnecessary fonts so that the list does not give away your real OS;
- change the screen resolution or page scale;
- disable or fake geolocation and WebRTC (to hide the real IP) in the settings;
- clear cookies and cache every time before logging in again;
- disable Canvas (using extensions like CanvasBlocker) or other “vulnerable” APIs in the browser.
This approach is not costly, but it is quite labor-intensive. You will have to constantly remember about dozens of settings, which is almost unrealistic for a workflow. If you miss even one little thing, the site will get the real parameter and compare it with your old fingerprint – the disguise will collapse.
Also, the combination of settings needs to be realistic. If you accidentally create an impossible mix (specify Windows, but leave macOS fonts), there will be issues.
Proxy (VPN) for IP change.
Many people think that all they need to do is hide their IP address and anonymity is assured. In fact, proxies and VPNs solve only part of the problem – the network part. Yes, your IP will be different. But all other characteristics of the device will remain the same.
If you went to a site without a VPN and then with a VPN but from the same browser, the fingerprint will match 90% of the parameters. The system is not fooled: it will realize that it is the same machine, just from a different address.
Antidetect browsers.
These are special services for complete fingerprint protection. They look like a regular browser (based on Chrome or Firefox), but allow you to customize the “legend” of your device. You can change dozens of parameters – from the banal User-Agent to subtleties like the list of media devices.
Modern antidetect browsers can generate safe profiles automatically: GoLogin can generate a fingerprint for the desired platform – just select a template and the program will set dozens of parameters (Canvas, WebGL, fonts, etc.) for you. If you want, you can edit all the values manually.
The advantage of antidetect browsers is that they isolate profiles from each other: each acts as a separate “computer” with its own unique data. However, you need to understand the subtleties of customization: without a competent approach, even the best antidetect will not save you if you create an obviously “left” fingerprint manually. Nevertheless, if used correctly, this tool is the most efficient and flexible way to change fingerprints on the fly.
How antifraud systems detect fingerprint spoofing
Of course, developers of anti-fraud algorithms are aware of the existence of antidetect browsers, and they aim to calculate the fact that the fingerprint has been tampered with. Here are some signs that raise suspicion:
An illogical or inappropriate IP address.
The most common mistake is that the user changes a lot of settings, but forgets the IP. Several accounts with different names but one IP will be quickly linked. Another situation is that the IP is changed to an “unsuitable” IP: for example, the account is positioned as local, but the proxy IP is in another country.
The geography of the fingerprint immediately spreads. Antifrod also takes into account the “quality” of IP: cheap proxies that have been used by hundreds of people (including malicious users) before you are often already on blacklists.
Mismatch between fonts and OS.
Different operating systems have unique sets of fonts. If you specify Windows in the fingerprint settings, but the font list contains macOS fonts, this is a clear signal of spoofing to the system. Even differences in the design of identical fonts can signal spoofing.
Browser type inconsistencies.
Every engine has small features that are visible to scripts. If your User-Agent claims to be Firefox, but under the hood is actually Chromium – sooner or later scripts will find a discrepancy. The same goes for versions. Websites with the help of test scripts can calculate that the browser is outdated, despite the “masking” in the UA line.
Abnormal device characteristics.
In an effort to uniquely personalize the browser footprint, sometimes hardware parameters – Canvas, WebGL, Audio – are changed to random values. But a fingerprint is not a collection of individual metrics, but a connected profile. If a combination of data as a whole is not found among real devices, it’s conspicuous.
WebRTC leaks.
Even if the main IP is changed correctly, the browser may inadvertently give out its real address via WebRTC. If the script sees two IPs – one from a proxy, the other local or ISP – it is obvious that the user is hiding something. Many anti-detect browsers allow you to disable or spoof WebRTC.
Mobile device emulation via desktop.
Smartphone footprints are very different from PCs: in terms of screen, performance, and available sensors. It is almost impossible to completely pretend to be a phone while sitting in front of a PC.
If antifraud “sees” that the browser is asked for mobile screen sizes, but lacks typical mobile sensors or typical camera resolutions, the profile will be flagged as suspicious.
Frequent print changes by a single user.
Finally, spoofing attempts themselves can be evidence. If an account has a new fingerprint every time it logs in that wasn’t there before, the system paints a picture: the user is changing devices like gloves or trying to hide something. In real life, people don’t jump between dozens of computers every day. So overly heterogeneous fingerprints signal multi-accounts or bots. Many platforms whitelist devices for each account – and logins from new devices require additional confirmation.
By combining these checks, antifraud systems successfully detect fake profiles. Naturally, no specific metric gives 100% certainty – the decision is made based on a combination of factors. Nevertheless, the better and more believable your fingerprint is, the less chance you have of attracting unwanted attention.
How to protect yourself from fingerprint tracking: expert tips
A few tips to help reduce the likelihood of being tracked by a digital fingerprint:
- Use a trusted antidetect browser. If your business involves multi-accounting or you have serious privacy concerns, a specialized browser is a must-have. Choose a reputable solution and update it regularly. This will make managing your fingerprints much easier and eliminate a lot of manual steps.
- Observe the consistency of the data. When setting up a profile, make sure that all parameters are consistent with each other. A simple rule of thumb: IP, time zone, language and geolocation should all point to the same country/region. Fonts and OS type should match each other. Browser version – match in User-Agent, Client Hints and the actual engine. Avoid non-standard screen resolutions and other “unique” settings that normal users don’t have.
- Don’t stand out by being too unique. In an effort to become anonymous, it’s easy to become even more visible. A unique fingerprint catches the eye of security systems. It’s better to look like everyone else than to have a perfect but one-of-a-kind profile. Don’t unnecessarily disable useful features (Canvas, WebGL), it’s better to add some noise via anti-detect than to remove a parameter completely. Fingerprint should be believable and similar to many others.
- Use reliable proxies and stick to a simple rule – one IP per profile. Saving on proxies will lead to a ban: a common or suspicious IP will ruin even the most elaborate imprint. Buy clean proxies from trusted sellers, match their geo to your accounts. Do not run multiple profiles through one address.
- Check your prints before you use them in your work. Before going online with a new profile, go to 2-3 checkers and analyze the results. If you see red flags (inconsistencies, low anonymity rating) – correct your settings. It is better to spend an extra 10 minutes on testing than to lose an important account because of a silly little thing. Also, periodically recheck your fingerprints – browser or OS updates can change something in your profile.
The future of device fingerprinting: upcoming trends
1. Tracking complexity.
Tracking methods will become even more subtle. New vectors are emerging: sensor data (accelerometers, gyroscopes), analyzing device performance or even micro fluctuations in equipment operation – all of which can theoretically add uniqueness.
Algorithms with AI elements are able to calculate the individual “handwriting” of a device based on a variety of barely noticeable features. Browser fingerprints will not disappear, but on the contrary – they will become more complex and comprehensive.
2.(Probable) regulations of fingerprinting laws.
Lawmakers are not standing still either. Regulators are already discussing restrictions on the uncontrolled collection of fingerprints – perhaps in the future, websites will be obliged to request consent for such tracking.
Major browsers are partially countering fingerprinting: Safari and Tor Browser are introducing cloaking (making all users as similar as possible), Firefox is blocking known scripts, and Chrome is experimenting with Privacy Sandbox to reduce the need for tracking. However, there is no direct ban, and the advertising market is still benefiting from any available technology.
3. Tracking will become heavier.
The arms race between anti-fraud and anti-detection will gain momentum. Tracking protection tools will become more and more sophisticated, and protection systems will increase their control (introducing additional checks, requiring verification at the slightest doubt).
Perhaps new solutions will emerge to identify us without invading our personal data, or vice versa – users will be given more control over their digital footprint. For now, browser fingerprinting remains a reality to be reckoned with and taken into account.
Conclusion – it is absolutely clear that the Internet will not become more surveillance-free in the coming years. We recommend being prepared for this today.
Conclusion
Remember that browser fingerprints in the right hands increase security, but in the wrong hands they compromise privacy. Always be aware of the footprints you leave online and apply protective measures sensibly.
The digital world continues to evolve and it is up to us to balance convenience, security and privacy.