Users are increasingly faced with a situation where they would like to maintain their anonymity, hide their IP address on the Internet and prevent third parties from accessing their personal data. There are many ways to hide the IP address: from simple and free to expensive, but guaranteeing the user 100% security on the network. Today we will get acquainted with a rather interesting topic, how to get around an IP ban?

Why avoid IP tracking?
Why avoid IP tracking? There can be many reasons for this, and first of all, it is a question of security and anonymity. Going to any site, any page, you leave your data on each server: what operating system, browser, its version, and most importantly, the IP address are used. You can accurately determine your country, city, district, and even the exact address by owning it. Everything would be fine, but using the same IP address and possessing knowledge in information technology, an attacker can access another computer and get the user’s personal information, passwords and do many unpleasant things.
But there are also more harmless things that force you to change your IP. The likelihood of encountering them is much greater. Recently, online advertising has become even more intrusive and sometimes even overly annoying. Moreover, in some cases, it pursues the same users on all sites where they go. If such advertising is extremely unpleasant, then one of the ways to escape from it is to get around an IP ban.
And what to do if you are unjustly banned on the game server or an interesting forum? You can try to log in from a different account, but now bans by IP are often practiced. They can only be bypassed by changing or disguising your real address. By hiding your address, you can cleverly download files from file hosting services with a limit on the number of downloads for one user.
There are some of the most popular examples when you need to hide your IP:
- For online payments. People buy a variety of products online, and not everyone wants what they buy to go public.
- To exclude tracking of user actions on the network. People don’t want anyone to know which sites they are visiting.
- To get around an IP bans on visiting certain sites and blocking. IP address spoofing solves this problem of blocking sites by law enforcement agencies and returns access to them from anywhere in the world.
- For safety. Bloggers, activists, and anti-corruption fighters often post provocative or revealing posts. They have to hide their IP so that no one can find out the address of their residence, name, surname, or other personal data.
- For entertainment or speculative purposes. IP substitutions are often used for practical jokes. It is also quite a powerful tool for winding upvotes in polls, buying reviews, and manipulating statistics.
In general, there are many useful uses for changing IP. And there are also many ways to change your address, and they all have their own characteristics and level of security/anonymity. We will now study them.
What is IP?
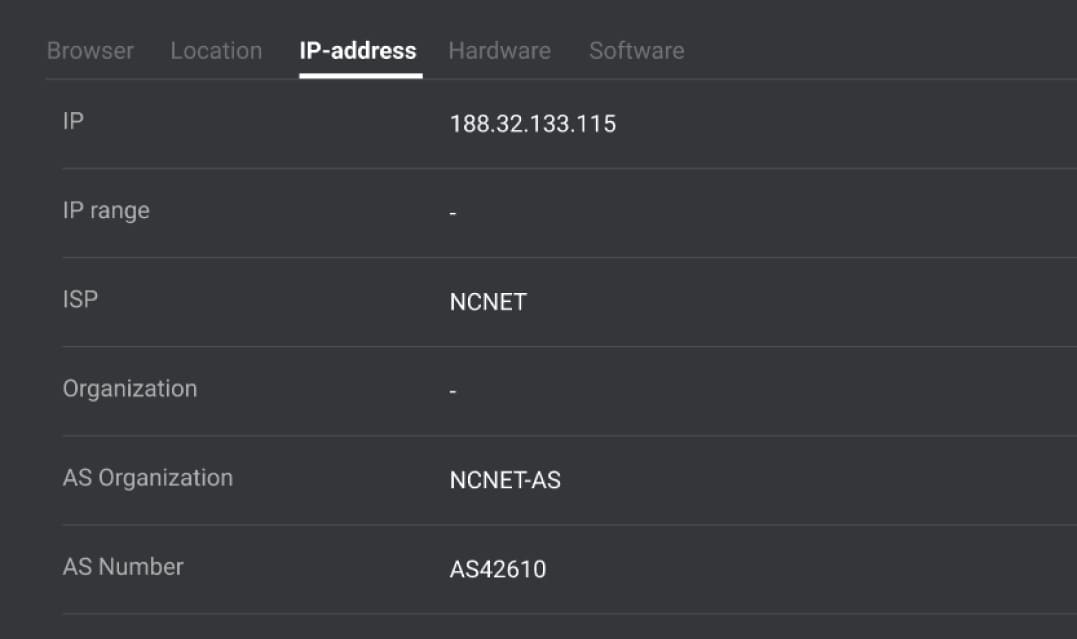
To get around an IP ban, you need to figure out three things. First, what is IP-address, where does it come from, and who exactly needs to be hidden from. And only then the scheme of hiding this address will become immediately clear.
An IP address is an identifier for a computer on a network that can send and receive IP packets, a type of message in Internet Protocol (IP). It is only needed so that other hosts can distinguish packets from different machines and send responses back to them. These addresses now exist in two forms (IPv4 and IPv6), but they have the same essence. Only the form of notation and restrictions (range) differ. The address is the main type of metadata used at the lower layers of the OSI model that powers the Internet.
Not all machines have an IP address, and it can be virtual (local, for example). A public IP address is issued to the device when it connects to the Internet by an Internet Service Provider (ISP). Companies operating in this sector have many such addresses at their disposal, which they buy in blocks of at least 1000 addresses. Every client on the network needs to be given a unique address, or they won’t use the network. Some companies issue it to the client permanently, some ISPs issue a new IP address to the client every time the connection is restarted (“dynamic IP”). As a result, your Internet address can only be changed by your ISP, and this process is usually automated.
How to bypass IP ban?
Before we take a closer look at the known technologies for hiding our real IP address, we should find out our IP address and find out some things that expose our computer on the network, for example, the address of the DNS server. To do this, go to any anonymity check service. The main thing is to check your computer with Java, ActiveX, Flash, and Javascript.
Changing your IP address, for example, using Socks or VPN, is not enough. Many technologies allow you to identify it, which you need to either disable on your computer or deceive. Also, it will not be superfluous to change the transmitted HTTP headers. It will “knock down” the definition of the installed software and the computer’s geographical location.
1. Proxy, SOCKS
A proxy server is a service on computer networks that allows clients to make indirect requests to other network services. First, the client connects to the proxy server and requests some resources located on another server. Then the proxy server connects to the specified server, receives the resource from it, and transfers it to the client.
Which servers and which protocols we can access through a proxy depends on the type of this proxy, that is, the protocol by which we access it. There are several types of proxies: HTTP proxies, SOCKS4, SOCKS5, and some others.
HTTP proxies are the most common, they are easiest to find on the Internet, but they only work with HTTP (there are also HTTPS proxies). Moreover, they can insert the client’s address into the request headers and be not anonymous.
The SOCKS protocol is most notable because it encapsulates the protocols of the application layer and the transport layer, i.e., TCP/IP and UDP/IP. Since it is only through these protocols that it is possible to work on the Web, through SOCKS, it is possible to work with any servers, including the same SOCKS, and thus organize chains of SOCKS servers. For the same reason, all SOCKS servers are anonymous – it is impossible to transmit additional information at the TCP/IP and UDP/IP levels without disrupting the superior protocol’s operation.
You can also highlight anonymizers – they look like a regular search engine, only instead of words/phrases, you need to enter the URL of the site that you would like to see in them. Anonymizers are scripts written, for example, in Perl, PHP, CGI scripts.
A couple of useful programs for working with HTTP proxies and sockets:
SocksChain is a program that allows you to work through a SOCKS chain or an HTTP proxy (you need to remember that any proxy server, and even more so a free one, keeps a log. And a person who has the appropriate rights can always figure out where you went and what you did, even if you use chains of 10 anonymous proxy servers in different parts of the planet).
FreeCap is a program for transparently redirecting connections through a SOCKS server for programs that do not have native SOCKS proxy support.

2. VPN (Virtual Private Network)
A VPN connection is not much different from connecting to a regular local network: applications will not feel the difference at all, and therefore, without any configuration, they will use it to access the Internet. When one of them wants to access a remote resource, a special GRE (Generic Routing Encapsulation) packet will be created on the computer, which will be sent in encrypted form to the VPN server. The VPN server, in turn, will decrypt this packet, figure out what its essence is (a request to download some HTTP page, just transfer data, etc.), and execute on its own behalf (that is, it will expose its IP) the corresponding action. Then, having received a remote resource response, the VPN server will put it in a GRE packet, encrypt it, and send it back to the client in this form.
Continuous encryption of transmitted data is key to ensuring security. PPTP traffic can be encrypted using MPPE (Microsoft Point-to-Point Encryption, supports 40-, 56- and 128-bit keys). It is a Microsoft protocol. The early versions were elementary hacked; in the new ones, gross errors were fixed, but Microsoft’s attempts to do something in the field of cryptography cause nothing but laughter. New versions of their protocols don’t get much-hacked analysis.
OpenVPN is a free implementation of VPN technology, organized based on the TCP/IP protocol stack generally accepted on the Internet. This ensures that the connection will work even with providers who do not support PPTP (most often, mobile operators who cut all GRE packets passing through GPRS and EDGE). Also, OpenVPN works even when you do not have a real IP-address, unlike PPTP, which requires the simultaneous establishment of two network sessions.
OpenVPN has a number of advantages over VPN technology:
Supports flexible client authentication methods based on certificates;

3. TOR
Tor (The Onion Router) is a free implementation of the second-generation onion router (the so-called “onion (multilayer) routing”). It is a system that allows users to connect anonymously, ensuring the transmission of user data in encrypted form. It is often viewed as an anonymous network providing anonymous web surfing and secure data transfer. With Tor, users will be able to remain anonymous when visiting websites, posting materials, sending messages, and working with other applications using the TCP protocol. Traffic security is ensured through the use of a distributed network of servers called “onion routers.”
Tor network users run onion-proxy on their machine. This software connects to Tor servers, periodically forming a virtual chain through the Tor network, which uses cryptography in a multi-layered way (analogy with onion).
Each packet that enters the system goes through three different servers (nodes), which are randomly selected. Before sending, the packet is sequentially encrypted with three keys: first for the third node, then for the second, and, finally, for the first.
When the first node receives the packet, it decrypts the “top” layer of the cipher (analogy with peeling an onion) and finds out where to send it next. The second and third servers do the same. At the same time, the onion-proxy software provides a SOCKS interface. Programs running on the SOCKS interface can be configured to work over the Tor network, which, multiplexing traffic, routes it through the Tor virtual chain, which ultimately allows you to provide anonymous surfing on the network.
There are special Tor add-ons for the Opera, Firefox web browsers.

4. SSH tunneling
SSH (Secure Shell) is a network protocol that allows remote computer control and file transfer. Uses algorithms to encrypt the transmitted information.
SSH tunneling can be considered a cheap VPN replacement. The principle of this implementation is as follows: all network software on the computer is forwarded to the designated port (your localhost), on which the service hangs, connected via SSH to the server (and as we know, the connection via SSH protocol is encrypted) and tunneling all requests; then all your traffic (no longer encrypted) can be forwarded from the server to a proxy (supporting tunneling) or socks, which transmit all traffic to the required addresses. The presence of a proxy is not required.
What are the advantages of this system:
- To organize this scheme, you do not need to install server software (since SSH account and socks can be easily obtained on the Internet);
- Because with an SSH connection, traffic is encrypted and compressed, then we get a small increase in the speed of work on the Internet;
- When the socks server is located on a different host, we get an additional chain of servers that increase our security and anonymity.

5. JAP
In one of the German institutions, a rather clever way of maintaining anonymity was developed. A special proxy program JAP is installed in the user’s system, which accepts all user requests for connections, encrypts (AES with a 128-bit key length), and safely sends it to a special intermediate server (the so-called mix).
The fact is that a huge number of users simultaneously use the mix, and the system is built so that each of them is indistinguishable from the server. And since all clients are the same, then it is not possible to calculate specifically one user.
Mixes are usually installed voluntarily, mainly at universities, which officially confirmed that they do not keep logs. Besides, chains of mixes are usually used (usually three mixes).

6. P2P anonymizers
Let’s look at the Peek-A-Boot network as an example. Peek-A-Boot is a distributed peer-to-peer network of computers owned by volunteers from different countries. The network was created so that users could bypass restrictions imposed by local censorship and gain access to Internet resources prohibited in a particular state.
Each node on the network is masked to send requests and receive information from specific IP addresses bypassing censorship barriers.
The user is connected to the ad hoc network where Peek-A-Booty operates. Several randomly selected computers access the website and forward the data to the person who sent the request.
All traffic on this network is encrypted using the e-commerce standard SSL, so it looks like an innocent transaction.
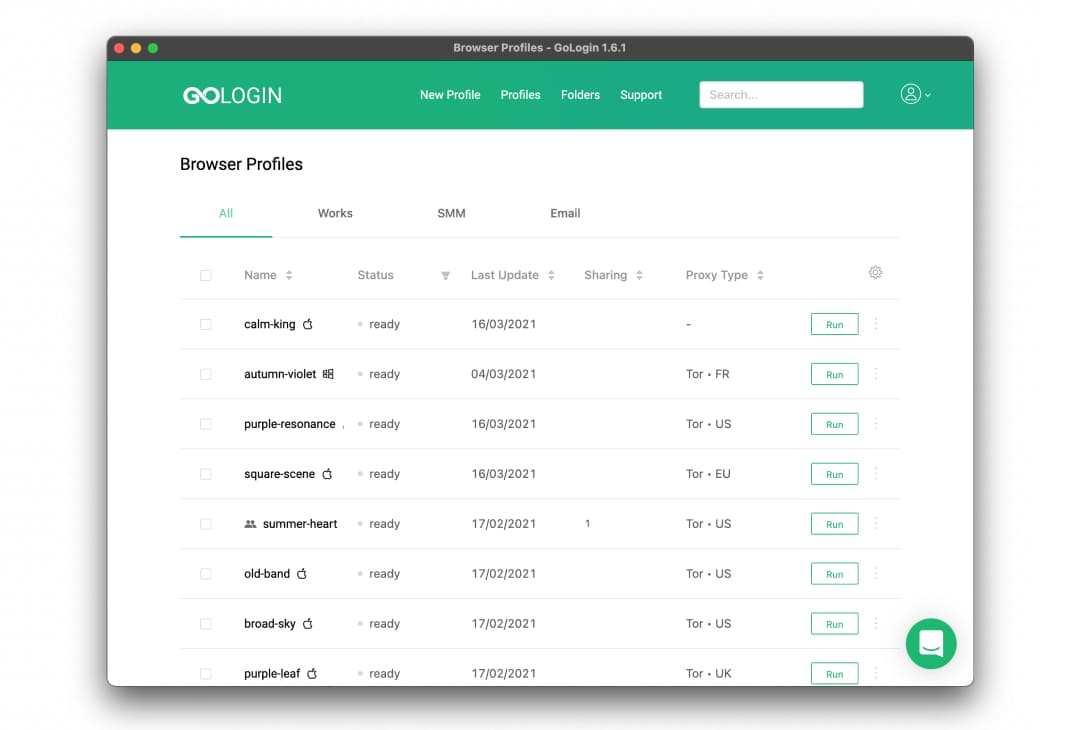
7. Anti-detect browsers
Based on what we wrote earlier, we can conclude that it is not enough to hide only the IP. After all, you can be tracked by other connection parameters. To solve this problem, anti-detect browsers have been created.
This software consists of a program that masks your fingerprint (including IP) and a browser that shows these parameters to the Internet.
Anti-detection browsers usually hide IP using proxy integration. But their advantage is that the rest of the connection parameters are adjusted to the new IP. It allows you to bypass IP bans, creating a completely different Internet identity. GoLogin is an example of a good anti-detect browser that will help you to avoid IP ban
Conclusion
Of all the methods we have considered, only TOR and P2P are completely free. Simultaneously, they are highly reliable, but, unfortunately, are not convenient to use and configure daily.
In terms of average security and ease of setup, OpenVPN leads the way, but prices start at $ 15 per month. The DoubleVPN technology, in which packets pass through two VPN servers, is now becoming widespread.
An intermediate solution can be SSH tunneling. It is enough to have only shell access, which is very cheap, and the connection itself is configured, for example, through Putty. Unfortunately, the setup is not easy and time-consuming, the usability is also poor, so this is still an option for geeks.
The safest and most anonymous way to bypass IP ban and mask other parameters is the anti-detection browser. It is perhaps the fastest and most convenient solution to the issue of guaranteed anonymity, but the price is the highest. But this solution is suitable for those who really need to bypass IP bans.


