Hoy en día, el tema de los servidores proxy es muy relevante y cubre una amplia variedad de industrias, estructuras y corporaciones. La gente busca los mejores servicios de proxy para programas de afiliados , privacidad personal , y otros propósitos. Este artículo describirá en detalle qué es un servidor proxy en términos simples, por qué lo necesita y cómo funciona. También hemos preparado una selección de los mejores servicios proxy y códigos promocionales ¡para ellos!

¿Qué es un servidor proxy?
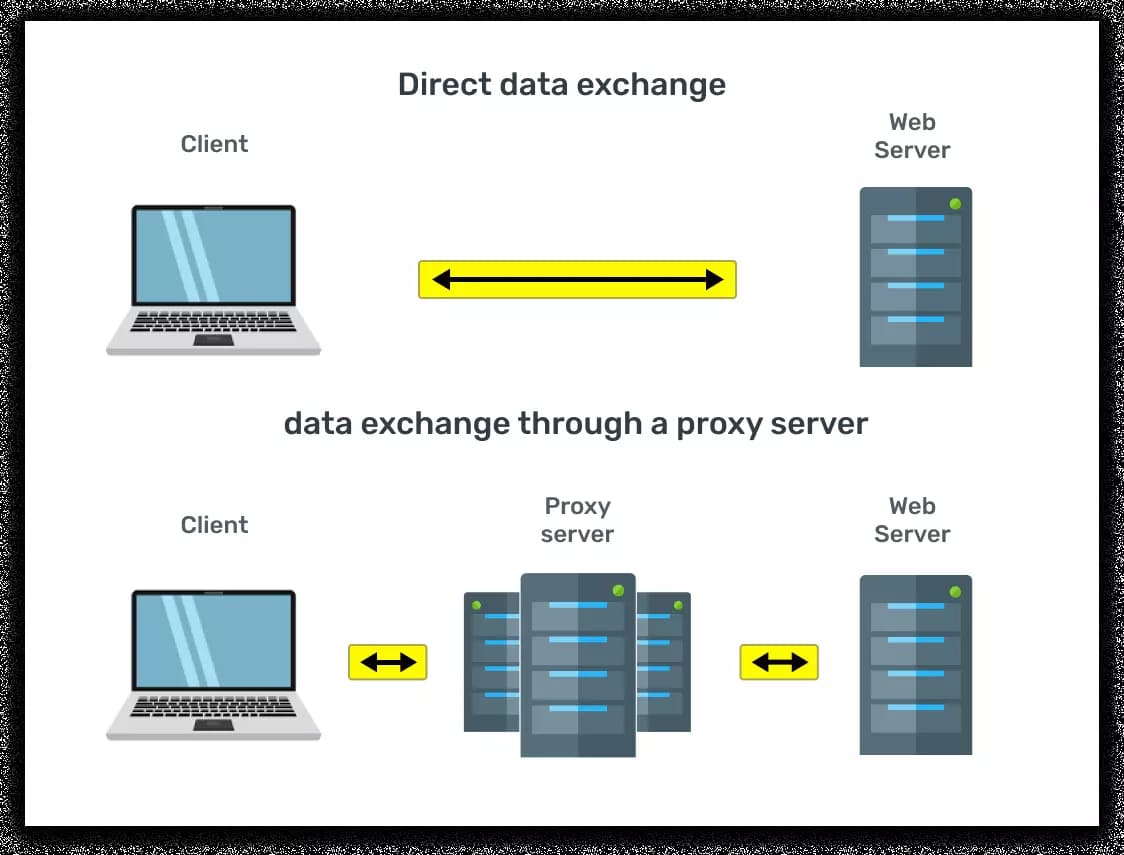
El servidor proxy es un servicio (software) que se ejecuta en una red y permite que una computadora realice solicitudes a otra en su propio nombre. Por lo tanto, el servidor proxy actúa como intermediario entre el cliente (por ejemplo, su computadora) y el servicio (por ejemplo, algún sitio de Internet) al que el cliente solicita acceso. La siguiente ilustración muestra esquemáticamente los procesos de intercambio de datos directos y el intercambio de datos utilizando un servidor proxy entre dos computadoras en la red .
¿Por qué necesitamos servidores proxy?
Hoy en día, los servidores proxy se utilizan principalmente para ocultar o cambiar la dirección IP al acceder a un sitio web. Puede haber muchas razones para hacer esto. Consideremos las más comunes.
- Acceso anónimo a sitios web. Se pueden usar servidores proxy anónimos, de élite y distorsionantes para navegar por la web anónimamente, descargar archivos, chatear en foros, correo electrónico y servicios de mensajería instantánea sin revelar su dirección IP.
- Para acceder a un sitio que limita la cantidad de conexiones o solicitudes por unidad de tiempo. Muchos servicios de intercambio de archivos limitan la cantidad de descargas de una dirección IP por unidad de tiempo. Teniendo en cuenta que muchos usuarios tienen IP dinámicas , puede surgir una situación cuando alguien que ocupaba la dirección IP que se te dio haya agotado previamente el límite de descarga del servicio. El uso de un servidor proxy ayudará a solucionar la situación. Asimismo, los proxies pueden ayudar a resolver el problema de usar servicios que limitan el número de peticiones
- Verificando el acceso al sitio desde todo el mundo. Usando un proxy, puede conectarse al sitio para verificar su disponibilidad desde diferentes países del mundo o proveedores y redes de Internet.
- Omitiendo bloqueos en línea. Con un servidor proxy, puede acceder a un sitio web al que no se puede acceder directamente debido a problemas de red o algún bloqueo. Por ejemplo, si la IP del usuario, o incluso todas las IP del país, son bloqueado en este servicio. También ayudará si el ISP del usuario deniega el acceso al sitio. Por ejemplo, en China, el acceso a algunos servicios populares de Internet está bloqueado, como Instagram, Gmail, Twitter, etc. Sin embargo, los usuarios de Internet en China puede acceder a ellos mediante servidores proxy ubicados fuera de China.
Tipos de proxy
Existen varios tipos de servidores proxy, cada uno de los cuales tiene sus características.
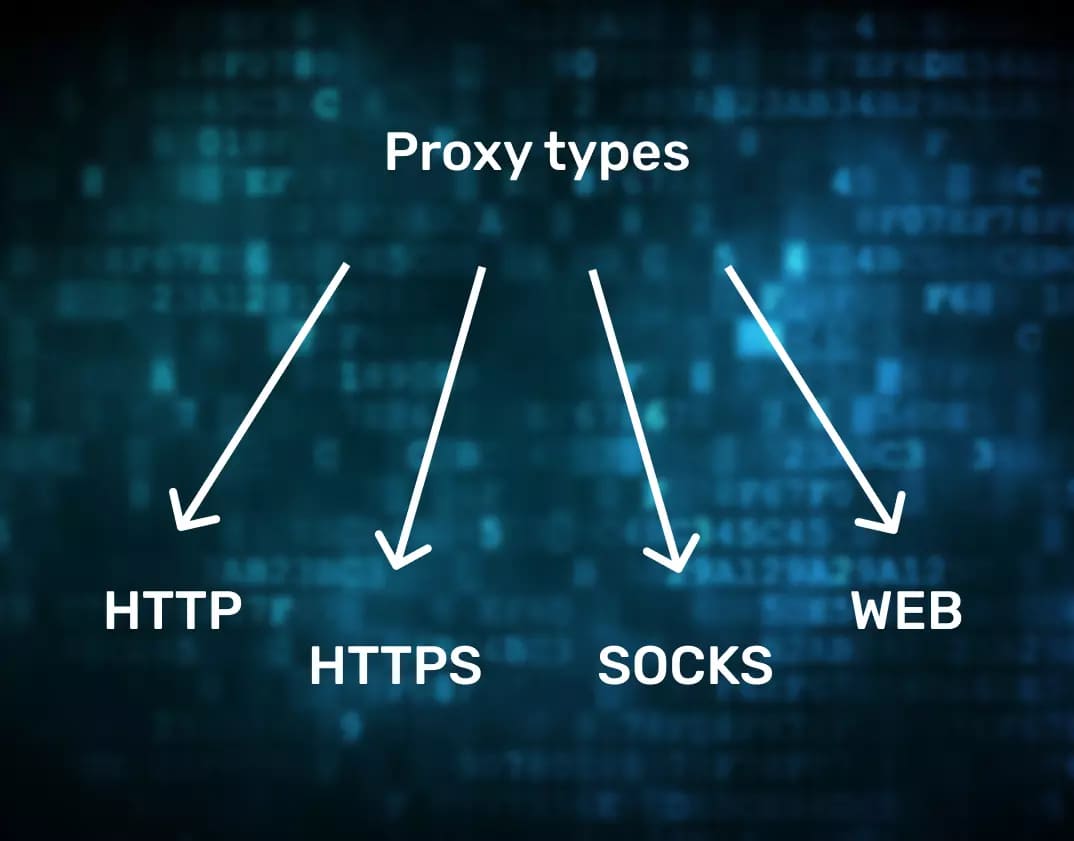
Proxy HTTP
Como sugiere el nombre, este tipo de proxy solo admite el Protocolo HTTP y es adecuado para navegar por la web y descargar archivos de servicios web que se ejecutan en el estándar Puerto TCP 80. Los proxies HTTP no son adecuados para navegar en un sitio que solo funciona con protocolo SSL seguro . Los proxies HTTP no se pueden encadenar. Desde el punto de vista de garantizar el anonimato, según el contenido de los encabezados HTTP enviados, los servidores proxy de este tipo se dividen en:
- Proxies altamente anónimos (elite). Los servidores proxy altamente anónimos no incorporan información del cliente y del proxy en los encabezados HTTP. Por lo tanto, el servidor no podrá determinar la dirección IP real del cliente y el hecho de que el cliente está utilizando un servidor proxy en general. Los servidores proxy altamente anónimos proporcionan el nivel más alto de anonimato;
- Proxies anónimos. Los servidores proxy anónimos transmiten información en los encabezados HTTP que indican que el cliente utiliza un servidor proxy (por ejemplo, el nombre y la versión del software del servidor proxy) pero no transmiten la dirección IP del cliente. Por lo tanto, el servidor podrá determinar que el cliente está utilizando un proxy, pero no determinará la dirección IP real del cliente. Los servidores proxy anónimos proporcionan un buen nivel de anonimato;
- Proxies distorsionados. Los servidores proxy distorsionados transmiten la dirección IP del cliente en los encabezados HTTP de forma distorsionada. Por ejemplo, solo muestran una parte. Por lo tanto, el servidor descubrirá que el cliente está usando un proxy y parte de la dirección IP real del cliente, que puede ser suficiente para determinar algunos datos sobre el cliente, como el ISP del cliente y su país y ciudad. Los proxys distorsionados proporcionan un nivel mínimo de anonimato;
- Proxies transparentes. Los proxies transparentes agregan un encabezado HTTP con la dirección IP real del cliente, para que el servidor pueda determinar que el cliente está usando el proxy y la dirección IP real del cliente. Los proxies transparentes no brindan anonimato.
Proxy HTTPS (CONNECT)
Los proxies de este tipo admiten el Método HTTP CONNECT , que habilita el túnel HTTP. En este proceso, el protocolo de capa alta (HTTP) se utiliza para transportar el protocolo de capa inferior (TCP). Estos proxies pueden conectarse a cualquier puerto. Por lo tanto, los proxies de este tipo pueden funcionan con casi cualquier aplicación de red (TCP), incluidos los servidores web a través del protocolo SSL seguro. En consecuencia, se denominan «proxies HTTPS «. El túnel HTTP garantiza el anonimato de los proxies HTTPS y les permite trabajar en cadena .
Proxy SOCKS
Casi cualquier aplicación de red puede funcionar a través del Proxy SOCKS . Por ejemplo, puede usar un proxy SOCKS para trabajar con su cliente de correo (protocolos POP3, SMTP, IMAP). Otra característica distintiva de los proxies SOCKS es que puede usar varios proxies SOCKS en una cadena a la vez , aumentando su nivel de anonimato. Los proxies SOCKS son siempre anónimos, ya que operan en un protocolo de bajo nivel y no actualizan los encabezados HTTP. Hay tres versiones del protocolo: SOCKS4, SOCKS4a y SOCKS5. La más funcional es SOCKS5. Permite para realizar consultas DNS en el lado del servidor proxy, utilice el protocolo UDP y el método BIND, abriendo un puerto para conexiones entrantes .
Proxy web (anonimizadores)
Un proxy web, también conocido como » Anonimizador «o «Proxy CGI «, es una página web que un usuario puede utilizar para visitar otro sitio web, en la mayoría de los casos de forma anónima. Los proxies web son fáciles de usar, ya que no es necesario cambiar la configuración del navegador. La mayoría de los proxies web admiten el trabajo con sitios sobre el protocolo SSL seguro. Los proxies web se pueden utilizar en cadena.
Tipos de proxy por restricción de acceso
Desde el punto de vista de un usuario de servidor proxy, cuantas menos personas tengan acceso a un proxy determinado, mejor. En primer lugar, cuanto menor sea el número de usuarios que utilizan un proxy en particular, mayor será su velocidad. En segundo lugar, infracción de las reglas para el uso de cualquier servicio en línea por parte de un usuario dará lugar a una prohibición, lo que hará que el proxy no sea adecuado para seguir trabajando con este servicio para todos los demás usuarios. Por lo tanto, los proxies de todo tipo se pueden dividir condicionalmente según el acceso limitado a ellos.
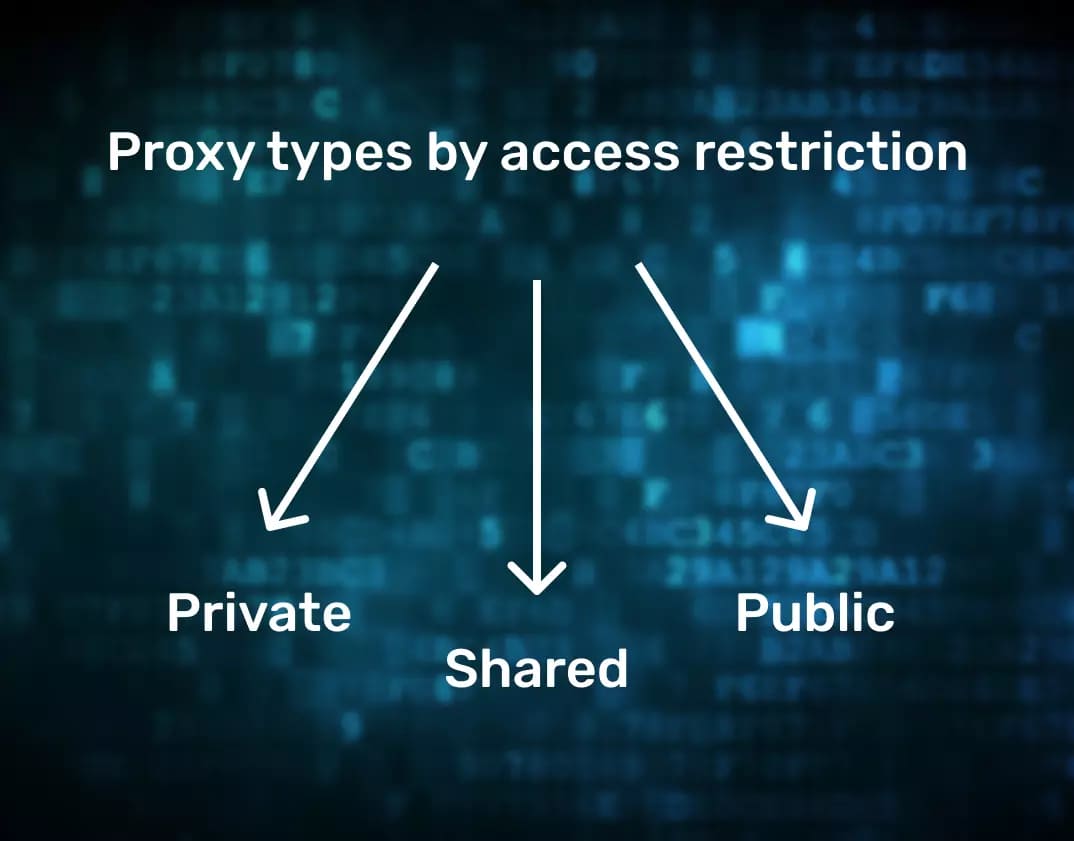
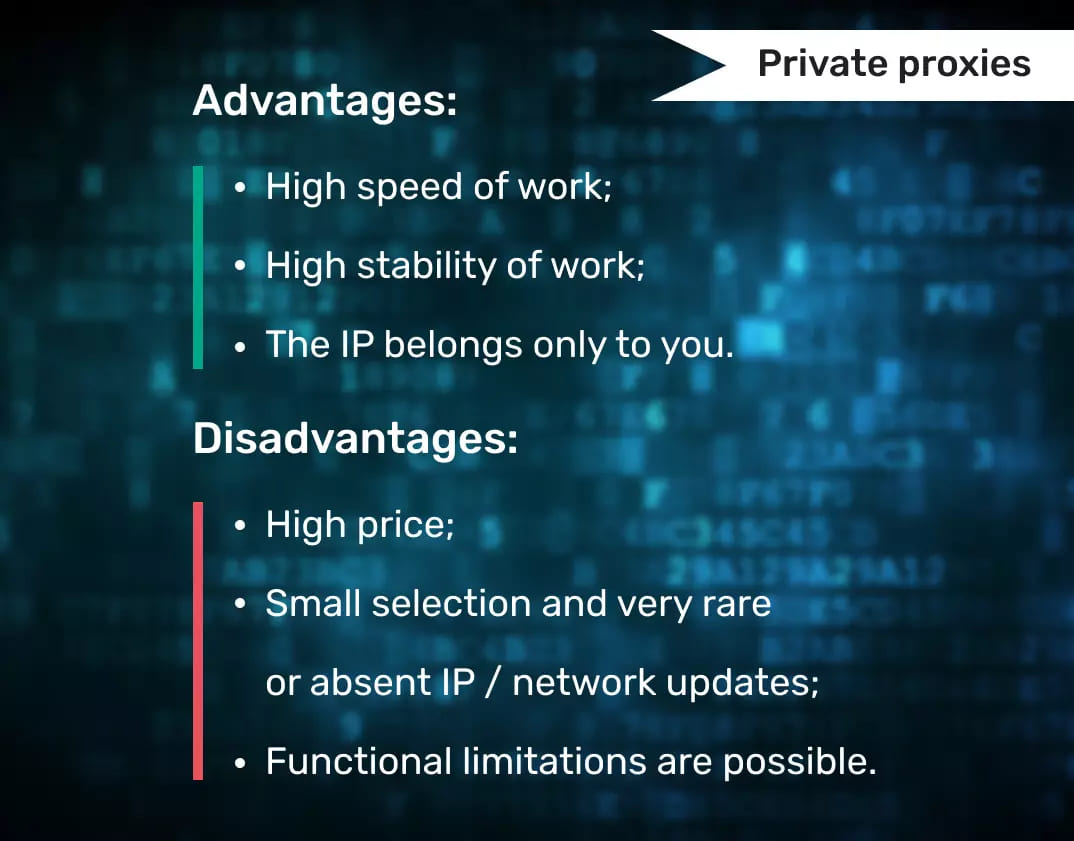
Proxies privados
Como sugiere la definición, los proxies privados son proxies que solo usa una persona. Por lo tanto, los proxies verdaderamente privados pueden ser llamados solo aquellos instalados en equipos al que solo usted tiene acceso, y el acceso a estos proxies está limitado por la autorización de IP. o nombre de usuario / contraseña. Solo en este caso, puede estar completamente seguro de que estos proxies son utilizados únicamente por usted .
Algunos servicios ofrecen proxies » con una sola mano «, y estos proxies serán privados para usted durante la duración del arrendamiento. Sin embargo, sería útil recordar que la calidad del trabajo con dichos proxies dependen de quién los usó ayer, antes que usted. Los proxies privados son más caros en el mercado que todos los demás, pero brindan, quizás, la estabilidad y velocidad de trabajo más excelentes en comparación con otros tipos de proxies .
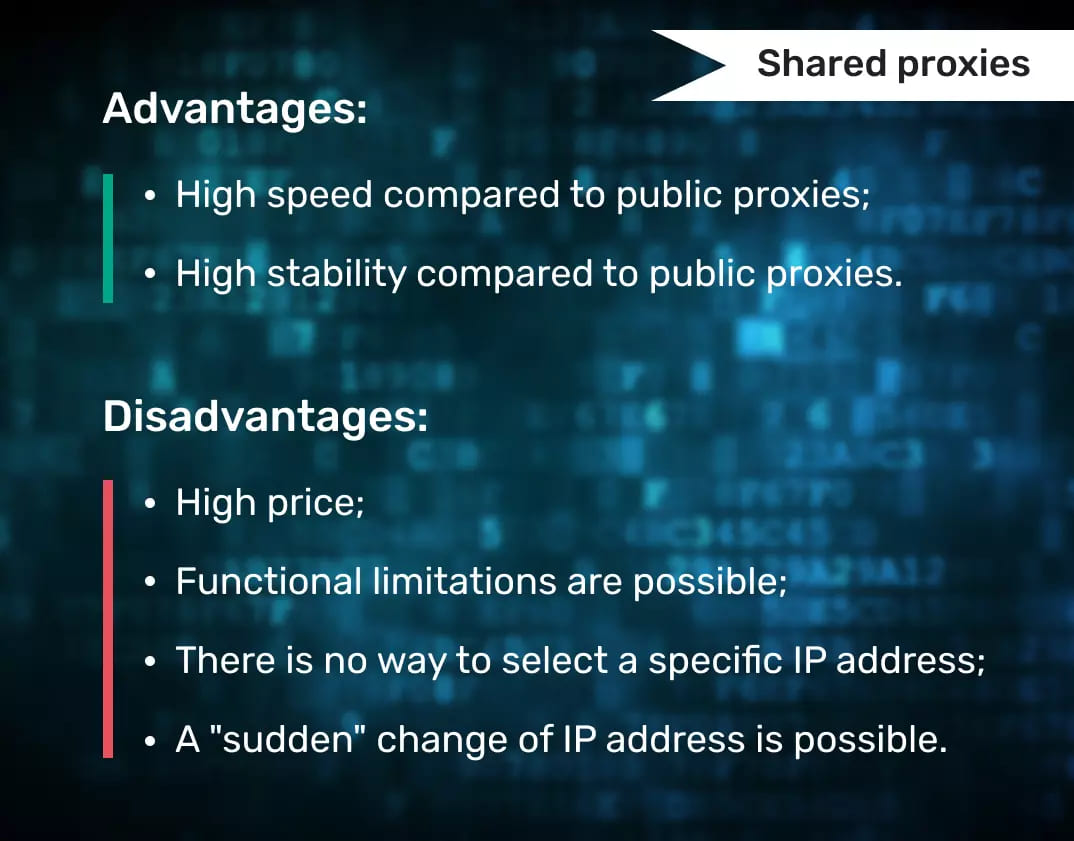
Proxies compartidos con acceso limitado
El problema de restringir el acceso a un proxy se puede resolver de diferentes maneras. El acceso al proxy puede estar limitado por el enlace de IP o por la autorización de inicio de sesión y contraseña. Esta solución la utilizan con mayor frecuencia los servicios que poseen el proxy proporcionado servidores. Estos proxies tienen una vida condicionalmente ilimitada .
Esta tecnología tiene sus inconvenientes para el usuario. En primer lugar, el cliente no sabe con qué dirección IP específica trabajará y, en segundo lugar, habrá un cambio repentino de la dirección IP cada 10-15 minutos. Los servicios que ofrecen tales proxies, por regla general, ofrecen miles, e incluso decenas de miles de proxies SOCKS en línea de todo el mundo a sus usuarios, que se pueden utilizar sin restricciones .
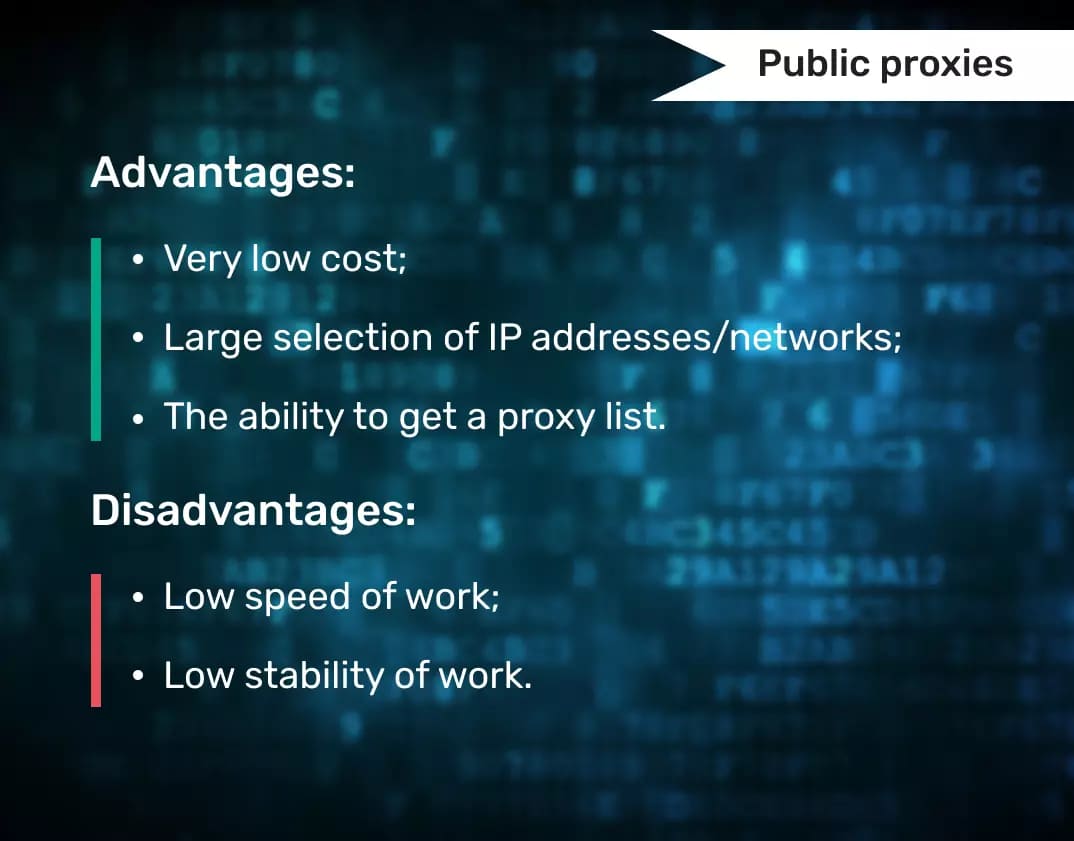
Proxies públicos
Las listas de servidores proxy públicos se cargan de forma gratuita en miles de sitios en todo el mundo. Tienen miles de servidores proxy, después de comprobar cuáles, según la fuente y la fecha de relevancia, funcionan aproximadamente el 5% de la lista.
Algunos servicios recopilan proxies de acceso gratuito y los verifican y clasifican regularmente, proporcionando acceso a listas de trabajo por una tarifa. El porcentaje de proxies de trabajo recibidos de dicho servicio es mucho mayor y puede alcanzar el 80%.
 La información es dinero. Es la razón principal por la que sus datos están en riesgo. Los anunciantes están buscando en el historial de búsqueda de su navegador; pueden beneficiarse significativamente de esta información. Supongamos que ingresa » apartamento en alquiler «o «comprar un apartamento » en la barra de búsqueda. Después de ver su historial de búsqueda, el anunciante sabrá que planea mudarse pronto. Es una excusa para mostrarle anuncios de taxis de carga, muebles, tiendas de materiales de construcción y compañías de seguros. .
La información es dinero. Es la razón principal por la que sus datos están en riesgo. Los anunciantes están buscando en el historial de búsqueda de su navegador; pueden beneficiarse significativamente de esta información. Supongamos que ingresa » apartamento en alquiler «o «comprar un apartamento » en la barra de búsqueda. Después de ver su historial de búsqueda, el anunciante sabrá que planea mudarse pronto. Es una excusa para mostrarle anuncios de taxis de carga, muebles, tiendas de materiales de construcción y compañías de seguros. .
Proveedores de proxy
Smartproxy
Website: www.smartproxy.com
Tipos de proxy : Centro de datos, residencial
Precios : $50 por mes
Puntuación de confianza : 4.5
Número de IP : 40,000,000+
Cobertura geográfica : 195+ países
Prueba gratuita : 7 días
Código promocional : ninguno
Smartproxy es un proveedor de proxy confiable y no juega. Ofrece una red de proxy de navegación anónima de primer nivel con la configuración más rápida disponible. Chatea con el equipo de asistencia, ya sea a las 2 a. m. o a las 2 p. m., raspa sitios web y limita la policía zapatillas de deporte de edición limitada con facilidad. Los planes son asequibles, el panel de control es intuitivo y el servicio está abierto a cualquier persona, desde un emprendedor hasta una empresa en auge.
Bright Data (former Luminati Networks)
www.brightdata.grsm.io/gologin
Tipos de proxy : Centro de datos, residencial estático, residencial, móvil
Precios : $15/GB Pago por uso
Puntuación de confianza : 4.5
Número de IP : 81,000,000+
Cobertura geográfica : 195 países
Prueba gratuita : Centro de datos, residencial estático, residencial, móvil
Código promocional : $250 al depositar $250 usando este enlace
Bright Data proporciona la red de proxy IP residencial más grande del mundo. Esta empresa se posiciona como el software de administración de proxy de código abierto más avanzado que le permite administrar sus proxies como un profesional sin necesidad de codificación, también gracias a su Proxy Manager. Todas las IP residenciales conocidas hoy en día han sido recopiladas por Bright Data.
The Social Proxy
Website: https://thesocialproxy.com/
Tipos de proxy : Mobile
Precios : 90EUR por mes
Puntuación de confianza : 4.6
Número de IP : Unlimited
Cobertura geográfica : 5 (US, Germany, UK, Israel and Austria)
Prueba gratuita : 24 horas
Código promocional : Gologin_TSP (15 EUR off)
El proxy social es un proveedor de proxy líder que desarrolla y produce proxies 4G residenciales. El proxy social se diseñó para resolver problemas de identidades en línea y permitir a los usuarios realizar de forma segura operaciones complejas como automatización, rastreo, eliminación y más. Ellos han ayudado con orgullo a nuestros socios a lograr índices de éxito incomparables, líderes en la industria, en sus campos
NetNut
Website: www.netnut.io
Tipos de proxy : Residencial
Precios : 300$ por mes
Puntuación de confianza : 3.8
Número de IP : 5,000,000+
Cobertura geográfica : 50+ países
Prueba gratuita : ninguno
Código promocional : GLNTNT (-15% descuento en todos los planes de proxy residencial)
NetNut es uno de los proveedores de navegadores proxy residenciales más rápidos. Utiliza los servicios de entrega de datos de DiviNetworks, lo que hace que la red de NetNut sea mucho más estable, segura y eficiente para navegadores anónimos. Esto se debe a que todo el tráfico se enruta a través de su red sin necesidad de un dispositivo de terceros. Como resultado, no habrá cuellos de botella, desconexiones o interrupciones en la red de proxy de navegación anónima.
GeoSurf
Website: www.geosurf.com
Tipos de proxy : Residencial
Precios : 450$ por mes
Puntuación de confianza : none
Número de IP : 2,521,459
Cobertura geográfica : 50+ países
Prueba gratuita : ninguno
Código promocional : GO50LOGIN (-15% para el paquete de inicio)
GeoSurf es uno de los mayores proveedores de navegadores proxy, con más de 2,5 millones de direcciones IP de ubicaciones de proxy en todos los países y ciudades del mundo. ¡Y sus direcciones IP nunca se detectan como proxies! Los administradores están disponibles para brindarle asistencia en todo momento. hora, todos los días, todo el año por teléfono, correo electrónico o Skype .
SSL Private Proxy
Website: www.sslprivateproxy.com
Tipos de proxy : Privado, Compartido
Precios : 15$ por mes
Puntuación de confianza : 4.1
Número de IP : 120,000+
Cobertura geográfica : 7 países
Prueba gratuita : ninguno
Código promocional : GOLOGIN25OFF (-15% para el paquete de inicio)
Uno de los nombres más importantes en la industria del proxy privado, SSLPrivateProxy ofrece proxies compartidos baratos y vírgenes para navegadores anónimos. Su red de proxy extendida también es una gran función si desea comprar direcciones IP geoespecíficas para anuncios clasificados sitios web o campañas de SEO locales .
Proxys.io
Website: www.proxys.io
Tipos de proxy : Privado, Compartido
Precios : $0.1 por mes
Puntuación de confianza : 4.1
Número de IP : 10,000+
Cobertura geográfica : 12 países
Prueba gratuita : ninguno
Código promocional : ninguno
Proxys.io es un servicio de alquiler de proxy con más de 10 mil direcciones IP de 12 países. El principal producto del proveedor son los proxies IPv4 e IPv6. Todos ellos pueden conectarse a través de los protocolos HTTP y SOCKS. El servicio también proporciona soporte las 24 horas del día y devolución de dinero dentro de las 24 horas posteriores a la compra. Todos los servidores proxy son como un software de navegación anónimo y no se realizan registros .
Proxy-n-VPN
Website: www.proxy-n-vpn.com
Tipos de proxy : Privado, Compartido
Precios : $1.35 por mes
Puntuación de confianza : 4.2
Número de IP : 10,000+
Cobertura geográfica : 3 países
Prueba gratuita : ninguno
Código promocional : ninguno
Proxy-N-VPN es una de las empresas líderes en proporcionar proxies anónimos con un alto nivel de seguridad para navegadores anónimos. La empresa ha estado operando desde 2012, la atención al cliente está disponible las 24 horas del día, todos los días del año. La velocidad del servidor es de 1000 megabits por segundo y puede devolver los fondos después del primer pedido en 3 días .
Oxylabs
Website: www.oxylabs.io
Tipos de proxy : Centro de datos, residencial
Precios : $180 por mes
Puntuación de confianza : 4.9
Número de IP : 102,367,458+
Cobertura geográfica : 185 países
Prueba gratuita : ninguno
Código promocional : ninguno
Oxylabs es uno de los mayores proveedores de proxies residenciales con más de 100 millones de direcciones IP residenciales repartidas por todo el mundo. Oxylabs tiene proxies residenciales en todos los países del mundo. Puede obtener un proxy de una ciudad específica ya que afirman tener apoderados en casi todas las ciudades importantes del mundo .
PrivateProxy
Website: www.app.privateproxy.me
Tipos de proxy : Centro de datos, residencial
Precios : $9 por mes
Puntuación de confianza : 4.5
Número de IP : no declarado
Cobertura geográfica : 4 países
Prueba gratuita : 7 días
Código promocional : GOLOGINAPP (25% descuento)
PrivateProxy.me es un proveedor de proxy que pertenece y es operado por Aqua Networks Limited, una empresa de TI con sede en Londres que se especializa en servicios de TI en la nube y proxy de navegación anónimo. La empresa se formó en 2010 y desde entonces ha prestado servicios a miles de clientes en todo el mundo. El mundo. Debido a su afiliación con una empresa de TI, PrivateProxy.me aprovecha los grandes grupos de recursos de direcciones IP que les permiten proporcionar proxies privados 100% limpios en muchos países del mundo para navegadores anónimos .
AstroProxy
Website: www.astroproxy.com
Tipos de proxy : Móvil, Residencial, Centro de datos
Precios : desde $0.55 por 100 Mb
Puntuación de confianza : 4.5
Número de IP : 1,000,000+
Cobertura geográfica : 20+ países
Prueba gratuita : 7 $ 2.35 a su cuenta, sin límites de tiempo, tipo, geo y número de proxies
Código promocional : ninguno
AstroProxy es una red de proxy de alta confianza que sirve proxies de tres tipos. Todos los proxies son dinámicos y se pueden cambiar dentro del grupo de IP seleccionado en cualquier momento.
Los proxies geolocalizados pertenecen a ISP nacionales y operadores de telefonía móvil. Por lo tanto, prometen una mayor seguridad y protección contra prohibiciones. Además, los proxies se clasifican fácilmente por país, ciudad e ISP o proveedor.
Todas las configuraciones y estadísticas están disponibles en una ventana.
AstroProxy funciona con paquetes de tráfico (100 Mb min) y no establece límites en el número o tipo de proxies. Obtiene un acceso completo a todos los grupos de proxy para cada puerto solicitado. HTTPS y SOCKS disponibles para todas las direcciones IP .
AstroProxy ofrece una prueba gratuita y un exclusivo programa de recomendación de RevShare. Más información aquí
LTEBOOST
Website: www.lteboost.com
Tipos de proxy : Centro de datos, residencial
Precios : desde $0.1 por mes
Puntuación de confianza : ninguno
Número de IP : 1,000,000+
Cobertura geográfica : USA, EU, RU, UA etc
Prueba gratuita : 7 Sí
Código promocional : BOOST (5% de descuento en todos los servidores proxy)
LTEBOOST son uno de los fundadores de los servidores proxy móviles 4G en la CEI. A partir de 2017, uno de los primeros en comenzar a conectar granjas de servidores proxy desde sus propios equipos y módems. Esta no es una red de botnet en la que corre el riesgo de ser pirateado por personas sin escrúpulos proveedores proxy.
Todos los servidores proxy tienen servicio en equipos LTEBOOST, la tienda de servidores proxy está registrada oficialmente como una entidad legal. Al comprar un servidor proxy de LTEBOOST, también obtiene soporte técnico competente, trabajo ininterrumpido, un gran grupo de direcciones IP móviles y residenciales. Todos sus proxies tienen rotación de direcciones IP externas, por lo que te liberarás de la compra constante de proxies estáticos.
FAQ
¿Es ilegal utilizar un servidor proxy?
Depende de las leyes de su país. Pero normalmente, si no utiliza servidores proxy para actividades ilegales, no tendrá ningún problema.
¿Es un servidor proxy como una VPN?
Para el usuario, la diferencia es que la VPN utiliza cifrado de extremo a extremo, los datos transmitidos son seguros desde el punto de entrada al punto de salida. Un proxy es una tecnología menos segura y no debe usarse sin un navegador antidetección
¿Un servidor proxy es bueno o malo?
Escribimos sobre todas las ventajas y desventajas de los diferentes tipos de proxies. En resumen, es importante tener en cuenta que usar solo proxies no le proporcionará un anonimato completo ya que los sitios monitorean otros parámetros de conexión. Por lo tanto, es necesario para usarlos con un navegador anti-detección que oculta otras huellas dactilares .
¿Los servidores proxy son gratuitos?
Hay servidores proxy gratuitos y de pago. Por lo general, cuanto más caros son, más anonimato y comodidad pueden ofrecer al usuario.
¿Cuál es el servidor proxy más seguro?
Los proxies más seguros son los que crea usted mismo en su hardware. En segundo lugar están los proxies privados.
Conclusión
Hay muchos proveedores de proxy en el mercado ahora, y cada uno de ellos proporciona diferentes tipos de proxies. Cada uno de ellos puede ser adecuado para resolver sus tareas específicas. No todo el mundo necesita proxies privados costosos. A veces, los públicos son suficientes. Por tanto, antes de elegir el tipo de proxy y proveedor, empieza por tus tareas. Te ayudará a encontrar la solución más eficiente